Value to Our Business: Sustainable Technological Solutions
Cybersecurity and Data Privacy

End-to-End Information Security Management

Integrated Information Technology Risk Management Structure
Ultimate responsibility for information security at Ziraat Bank rests with the Board of Directors, while implementation at the Group Presidency level is carried out by the Internal Systems Group Presidency.
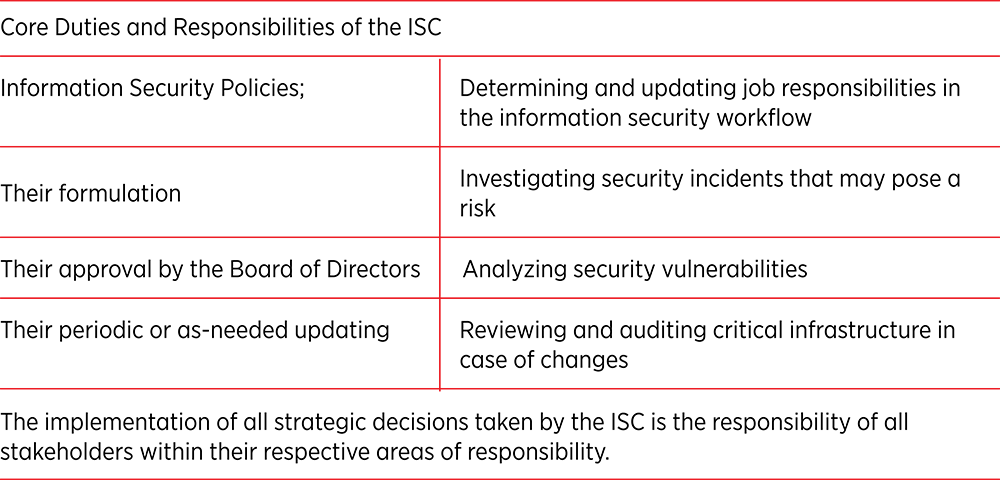
The coordination and management of projects designed to ensure compliance with the Banking Law, the Articles of Association and other relevant legislation concerning information security, within the framework of the policies and strategies established by the Board of Directors, are conducted by the Information Security Committee (ISC).
The Bank considers Information Technology (IT) risk to be a critical component of its enterprise risk structure and operational activities. In this context, risk management is carried out effectively through the review of the Presidency of the Republic of Türkiye Digital Transformation Office Information and Communication Security Guide, the BRSA Regulation on Banks’ Information Systems and Electronic Banking Services, as well as other applicable regulations and best practices. The ISC is responsible for ensuring that these processes are conducted in alignment with the Bank’s strategies, for overseeing planning activities and for managing related actions.
An integrated IT Risk Management framework has been established in alignment with the strategies and policies in place. By managing this governance structure in an integrated manner with its technology company, the Bank minimizes the impact of operational risks that may threaten business continuity and data integrity.
Leveraging international standards, the Bank has defined risk measurement parameters and key risk indicators. By designing system enhancements and user interfaces that enable proactive and continuous monitoring of risks exceeding defined threshold values, the Bank makes it possible to conduct root-cause tracking, monitor implemented control activities and obtain consolidated reports on these activities.
For the purposes of processing, storing, transmitting, protecting and ensuring the continuity of information produced, the Bank defines all assets of value to the Bank as “information assets”. In line with the “Regulation on Banks’ Information Systems and Electronic Banking Services” published in 2020, all information assets are classified based on confidentiality, integrity and availability criteria. Attributes such as the owner, custodian and location of each asset are recorded. In addition, rule sets governing the use of these assets are established, and procedures are implemented for physical transfer and disposal where required.
Within its risk management process, Ziraat Bank analyzes classified information assets according to their security value and determines security controls based on the criticality of these assets. The assigned security controls are assessed through testing, and based on the test results, corrective measures are implemented with the aim of reducing outcomes below the defined threshold level.
Under the umbrella of the ZFG, projects are ongoing to standardize the risk culture across all overseas subsidiaries and branches and to establish a single, consistent risk framework. Employees within the Group have information security obligations in cases of onboarding, termination or changes in role. Access rights are assigned through systems automated via the Identity Management Application, and an Identity Management Policy is established with a focus on the principle of least privilege and segregation of duties.
Information Security Awareness Program
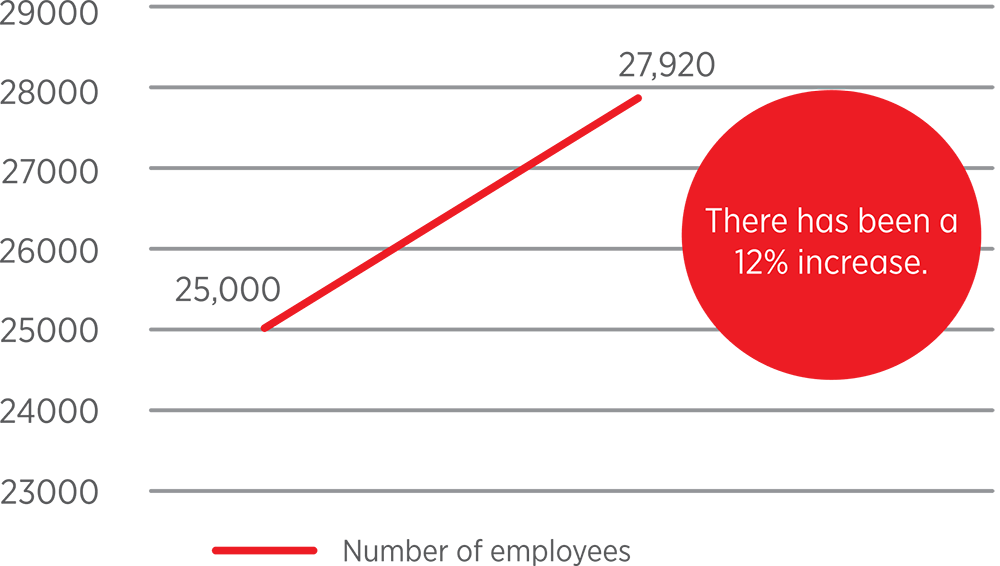
ZFG has established a comprehensive “Information Security Awareness Program” for all employees in order to foster a high level of awareness and consciousness regarding information security. Within the scope of the program, information security bulletins are published on a regular monthly basis, and surveys are prepared to assess employees’ awareness of information security risks. In addition, internal drills are conducted using social engineering methods to build a culture of avoiding phishing attacks. In 2025, 16 phishing tests were carried out. Based on the outcomes of these drills, the necessary trainings are assigned to enhance employees’ level of awareness.
For newly hired employees, information security trainings are delivered in a face-to-face format as part of orientation programs. In addition, trainings assigned throughout the year aim to maximize employees’ awareness and knowledge levels.
In 2025, face-to-face training was provided to 975 employees who joined the Bank during their orientation period, while remote training was delivered to 27,920 employees across the Bank.
Security Technologies Supporting Value Creation
Ziraat Bank conducts information security enhancement initiatives not only for its employees but also for other stakeholders across its value chain, including customers, service providers, business partners and other third parties. Aware of risks arising from the human factor, the Bank regularly informs its stakeholders about cyber threats frequently employed by threat actors, such as phishing, malware, identity theft and social engineering attacks. Within this scope, supplier-related risks are monitored based on data obtained through the “Third-Party Risk Surface Service,” and targeted awareness communications are repeated when necessary. Through these efforts, the Bank aims to strengthen stakeholder trust while ensuring operational continuity.
To remain continuously prepared against potential cyber threat actors, ZFG has established a Cyber Security Center operating uninterruptedly, seven days a week. This structure analyzes banking systems and alarm mechanisms, performs vulnerability scanning and gathers cyber threat intelligence to enable timely response actions.
Network and endpoint security products and devices - including DDoS protection, IPS, EDR/EPP systems, NAC and WAF systems, firewalls and email security solutions - together with Data Loss Prevention (DLP) systems designed to prevent data leakage, Web/DNS security systems, Security Information and Event Management (SIEM) systems capable of monitoring all security logs and generating alerts, application code review systems, penetration testing tools and vulnerability management systems operate continuously and without interruption. Network traffic on employee devices is continuously monitored, and internet access rules are configured via proxy systems based on user profiles. Role-based authorizations are established in accordance with the segregation of duties principle, and system logs are transferred to the SIEM platform. Alerts are generated for transactions that deviate from defined authorization schemes, enabling rapid response through advanced monitoring systems.
In 2025, Ziraat Bank carried out integration efforts between its Active Directory infrastructure and security solutions to enable more effective management of vulnerabilities and exposures, while update activities for Breach and Attack Simulation (BAS) modules continued within this scope. In addition to these technologies, the MISP (Malware Information Sharing Platform) technology was put into operation as of 2025, enabling centralized management of cyber threat intelligence. Furthermore, integration efforts are ongoing to enable the centralized management of SIEM systems across overseas subsidiaries and branches through a single platform.
Legal Compliance and Assurance Mechanisms in Information Security
In light of national and international laws, regulations, decisions and directives issued by regulatory authorities affecting information security, the Bank evaluates the risks associated with each identified information asset within a framework aligned with international standards. In this context, each risk is assessed within a legally grounded and auditable structure based on applicable regulatory requirements. While establishing its regulatory compliance framework, ZFG has relied on nationally and globally recognized standards and models. Key references include, but are not limited to, the following:
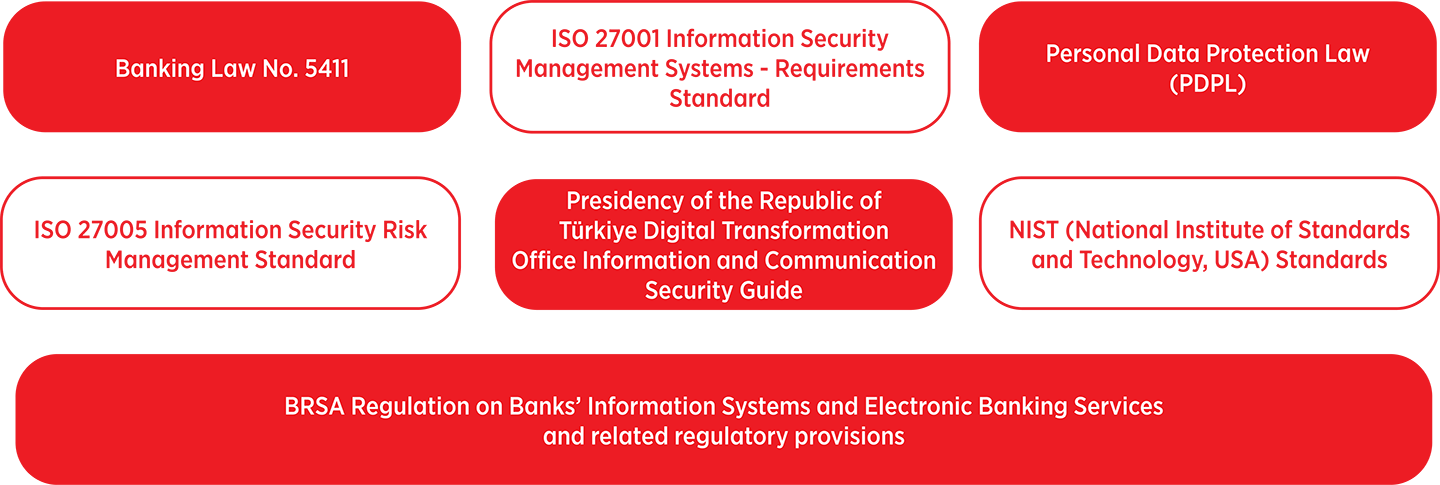
Information security policies of Ziraat Bank and all its subsidiaries, together with the legal documents supporting these policies, are prepared in compliance with the regulations established by supervisory and regulatory authorities. These arrangements are also periodically reviewed in line with digital transformation initiatives, technological advancements and developments in business processes.
The Bank implements the necessary procedures and safeguards to ensure the secure storage of personal data, prevent unlawful processing and enable lawful destruction where required. Within the scope of the disclosure obligation set forth as a mandatory provision under the Personal Data Protection legislation, the required disclosures are provided, and particular care is taken to obtain explicit consent through all customer contact channels. To enhance awareness in this area, mandatory trainings on personal data protection are delivered to employees through both classroom-based and remote learning formats.
In accordance with the BRSA Circular on Penetration Tests for Information Systems, penetration testing is conducted at least once annually by independent firms with no executive role within the ZFG. Based on the results of these tests, areas requiring improvement are identified, findings are reported to the Board of Directors, and the necessary action plans are established.
To protect against threats originating from both internal corporate networks and external networks, ZFG implements Network Security Control Systems. Within the framework of Bank policies, rules are established governing devices and access provided to non-bank personnel working at Bank locations - including third-party employees, consultants, independent audit firms and external auditors - covering areas such as USB usage, external file sharing, database and application access, and restrictions on the installation of non-standard applications. The use of network resources is monitored through Data Loss Prevention (DLP) systems to prevent data leakage in accordance with defined rules and policies.
Compliance with International Standards in Information Security Policies
Ziraat Bank conducts its information security processes in alignment with international standards. The Bank grants users access only to the networks and network services for which they are authorized and revokes such authorizations once the relevant business need ceases. Through established password policies, confidential and sensitive information is protected on an individual basis, and information sharing is permitted only through secure and dedicated channels. Security procedures are further strengthened through masking, blocking, monitoring and encryption techniques applied within data processing activities.
Services procured externally that may affect the confidentiality, integrity and availability of data and potentially disrupt business continuity are defined as “Outsourced Services". In order to minimize supplier-related risks under outsourced service arrangements, Ziraat Bank incorporates information security requirements into procurement specifications and contractual agreements. Supplier companies providing such services are regularly evaluated within the scope of confidentiality agreements.
Robust Cybersecurity Structure
Within the Bank, the information security infrastructure is managed at the highest level through the Internal Systems Group Presidency, operating under the authority of the Board of Directors. Management units within this group perform information security controls, and action plans are developed in coordination with relevant business units.
Ziraat Bank maintains a Cyber Incident Response Team (CERT) to ensure that information security incidents are managed rapidly, effectively and systematically, and that necessary response actions are implemented. All information security incidents and vulnerabilities are recorded through centralized monitoring mechanisms. Each recorded incident is managed in accordance with the Information Security Incident Management Plan based on its level of criticality and incident type, and necessary action plans are implemented promptly.
During 2025, Bank systems were exposed on average to approximately 600,000 spam or malicious emails and more than 400,000 network-based attack attempts per month, including various Distributed Denial of Service (DDoS) attacks and unauthorized access attempts. No data leakage incidents occurred during 2025. The Bank’s information security framework is subject to regular annual audits in accordance with the BRSA Regulation on Banks’ Information Systems and Electronic Banking Services. In line with the Regulation on the Data Controllers’ Registry, the Bank registers and discloses the data it processes as a data controller in VERBİS. Detailed disclosures and privacy notices related to the Bank’s Data Processing Policy are available on the corporate website.